In any organization, there are set duties, assignments and responsibilities to accomplish department goals, targeted objectives, and outcomes. Employees at every level within a business organization should take their responsibilities about Cybersecurity very seriously and be part of the organization Cybersecurity focus. Every department under the business structure should know what their part within the organization cybersecurity program. Every one, though matter what department they belong to should work as a team to meet and exceed the organization cybersecurity goals. Having a great cybersecurity program is the responsibility of management and it should be a part of every facet in all sectors of the business. In every organization with an IT department, the IT department is the regulator of the business cybersecurity program. They create the policy, in accordance with the business goals, mission, and objectives. They build, implement and monitor the organization cybersecurity program against the business set goals. Continue reading
Information Technology
History of Memory and Storage Systems
As we know the memory is a power to remember things. In psychology, memory is the process by which information is encoded, stored, and retrieved. But in computing, memory refers to the physical devices used to store programs or data on a temporary or permanent basis for use in a computer or other digital electronic device. Computer data storage, often called storage or memory. It is a core function and fundamental component of computers. A computer’s memory can be said as a list of cells into which numbers can be placed or read. Each cell has a numbered “address” and can store a single number. In almost all modern computers, each memory cell is set up to store binary numbers in groups of eight bits. A bit is the basic unit of information in computing and telecommunications. A bit can have only two values, either 1 or 0. Eight bits Continue reading
Artificial Intelligence vs Human Intelligence
Artificial Intelligence is the art of programming computers in order to produce intelligent behavior, whereas brain theory is the study of the brains function, to understand how the brain functions, the stimulations that go within and how outputs are produced via mathematical modeling and computer stimulation. It can be argued that both contain similar characteristics for functionality, both works together, this can be seen through artificial intelligence used to understand the roles of brain mechanisms. Furthermore both are involved in high cognitive task, such as reasoning, problem solving and decision making. Although some philosophers have accepted that machines can do everything that humans can do, some disagree with this view arguing that such high sophisticated behavior such as love, emotions discovery and moral decisions can only be carried out by humans. AI for many years has been pursuing the study of intelligent behaviour, but using artificial methodology. Intelligence can be Continue reading
Enterprise Service Bus (ESB) – Explanation, Role, and Functions
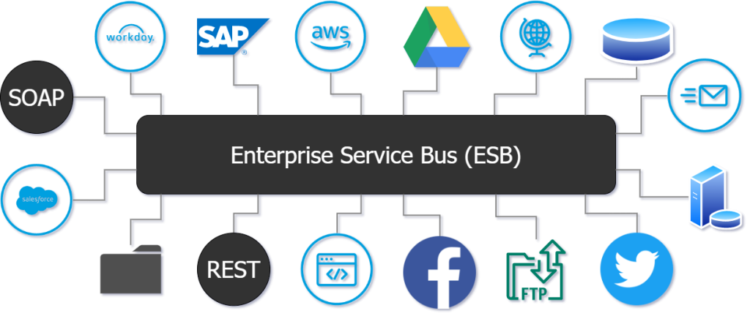
Before the emergence of service-oriented architecture (SOA), the term middleware would often be equated with an application server. However, today with the degree of progress on service-oriented architecture the term middleware will often be equated with Enterprise Service Bus (ESB). This is because if the application server is the foundation for middleware then ESB represents the largest and most important part of middleware in Service Oriented Architecture. Enterprise Service Bus (ESB) is a term used to describe a wide variety of products whose primary goal is to extend the simple messaging capabilities of an application server to allow the inclusion of enterprise functionality needed to support SOA. It has also been observed that a major difference between ESB and middleware is the fact that ESB is Service-Oriented whereas middleware has functions that are applicable outside the realm of services in a distributed system. The ESB can accomplish business communication by Continue reading
Classification of Security Threats in Information Systems
As use of internet and related telecommunications technologies and systems has become pervasive, use of these networks now creates a new vulnerability for organizations or companies. These networks can be infiltrated or subverted a number of ways. As a result, organizations or companies will faced threats that affect and vulnerable to information system security. Threats to information system can come from a variety of places inside and external to an organizations or companies. In order to secure system and information, each company or organization should analyze the types of threats that will be faced and how the threats affect information system security. Examples of threats such as unauthorized access (hacker and cracker), computer viruses, theft, sabotage, vandalism and accidents. Unauthorized Access (Hacker and Cracker): One of the most common security risks in relation to computerized information systems is the danger of unauthorized access to confidential data. The main concern comes Continue reading
Introduction to File Organization
As in our daily life, huge amount of data has to be collected and processed, so it is very difficult to handle it. But this can be handled fast and easily by using files. Files are the mega byte data structure used in information processing. Actually, a file itself is a bunch of bytes stored on some storage devices like magnetic disk, magnetic drum and magnetic tape etc. A file is a collection of records. Each record is made up of fields. The various fields consists of groups of characters, say the decimal digits 0 through 9 and alphabet A through Z. Group of fields are combined to form a logical record. This logical record contains all the data of interest about some entity. Different application requires a variety of record types and file structure; one basic distinction is between fixed and variable length records. A fixed length record has Continue reading